Home
Welcome to the wiki Multi File Fuzzer.
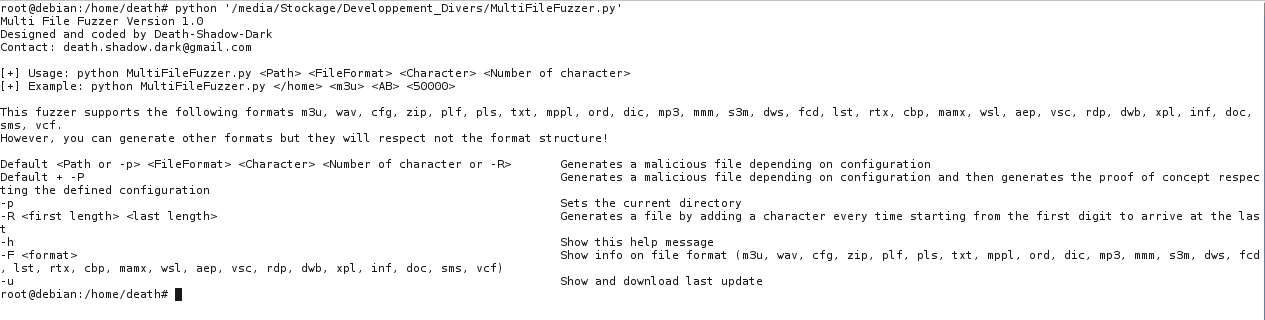
Multi File Fuzzer developed in python, so he needs the Python Framework. You can download the official site: http://www.python.org/download/. It is possible that Python is installed by default on your operating system.
The purpose of Multi File Fuzzer is to help developers and auditors to detect vulnerabilities in their applications. The advantage of this tool is that it incorporates the structure of the format (header, footer, ...). Multi File Fuzzer supports 33 different formats: m3u, wav, cfg, zip, plf, pls, txt, mppl, ord, dic, mp3, mmm, s3m, dws, fcd, lst, rtx, cbp, mamx, wsl, aep, vsc, rdp, dwb, xpl, inf, doc, sms, vcf, mef, asz, dal, png.
To use Multi File Fuzzer, you must follow the following example: python ./MultiFileFuzzer.py Path FileFormat Character Number_of_character
- Path: You must put the folder in which the malicious file will be stored, example: "/home"
- FileFormat: Vous devez choisir un format parmi la liste ci-dessus ou à un autre format (à noter que si vous mettez un format différent, la structure ne se conformera pas), par exemple: m3u
- Character: You need one or more character(s) to be used for malicious code, example AB
-
Number_of_character: The string selected above will be added as many times as the value you put in this variable. If you set this variable to 5000, the string AB will be multiplied by 5000 in the malicious file, example 5000
-
The command -h show help.
- The command -u show last update.
- The command -p load the current directory (Can go instead of "Path").
- The command -F <format> shows the information format.</format>
- The command -P can be added at the end of the default command to generate proof of concept.
- The command -R <first length=""> <last length=""> substitute "Number_of_character". Generates a file by adding a character every time starting from the first digit to arrive at the last.</last></first>


