Interoperability: facing invisible enemies with a blockchain-based digital identity
A newly released report from the British company Juniper Research shows that “SSI (self-sovereign identity) movement, which uses blockchain to give users direct control of who accesses their online credentials, will reach annual revenue of $1.1 billion by 2024. This is up from an expected $100 million by the end of 2020”, as we can read from the press release published by the same company.
Digital trust? Absolutely! However, let us analyze some key-facts before.
February 2020. The dramatic spread of COVID-19 suddenly stopped every human contact for at least two months, running into the risk of a second wave in Fall 2020. Facing a pandemic in the twenty-first-century was not just a heroic action according to the safety hygiene measures, but what annihilated us more was avoiding every human contact. Because of isolation, the social contact has been increasing in the digital world. Things taken for granted are not anymore, so now the question: how are we supposed to prove we are worthy of trust even if we communicate through a digital portal?
This taught us how humans had to face invisible enemies and how strong our need for proofs of credibility is. During this challenging time, many solutions have been tried. However, the one that seems most likely to make a difference is a blockchain-based digital identity, based on the SSI (self-sovereign identity) principle using the novel DID protocol.
How do we solve this problem?
The rising standards concern having a “digital identity”. Fundamental concepts of digital identities are the self-sovereign identity (SSI) and decentralized identifiers (DID). Why are they so important, and why right now? Due to the pandemic, many companies need to show they have proofs of being secure and trustable, and that is why they need to adopt the SSI protocol.

However, before getting deeper into the theme of self-sovereign identities and explaining why the blockchain-based digital identity may make an essential difference today, we need to clarify some fundamental concepts. The first one is the word “identity”: how can such a human connotation relate to the technological and digital world? In the twenty-first century, identities are not just referring to a flesh and blood person. Due to societal and technological development, we have been considering other ways to express our identities, such as through the digital world.
Personas, identifiers, and digital identity
Identities are built by many other little frameworks, which, scientifically, are called “personas”. According to the scientific studies of the mind and behavior, “persona” is a fundamental concept to understand how identities work. A persona is a subset of personality, depending just on one nuance. A person can have many personas, according to social context, work, friends, interests, hobbies, etc. Like the pieces of a puzzle, multiple personas build a unique identity.

As a result of the twenty-first-century society we grew up in and live in, we could count accounts as personas. To authenticate our-selves, we use usernames and passwords. However, most of these administrative identity systems are owned by the organization they are provided by. Some examples could be the user-centric approach of Google or Apple sign-in, which will just redirect you in their system again. Which is the problem here? The user is not in control of his digital identity with the risk of identity fraud or being hacked, as happened to Equifax’s customers in one of the biggest breaches in history.
What happened to the Equifax’s customers and why? March 2017. Hundreds of millions of identifying data were stolen from the American financial company. The company was hacked through the consumer complaint web portal, and the attackers could steal usernames and passwords because the systems were not adequately segmented from one other. The web portal was not secure enough so that the attackers could sneak into the system.
It is also essential to define “identifiers” since they are not supposed to qualify a person, but to be used to correlate to a “real-world identity”. Identifiers are usually assigned by a third-party and refer to a specific use domain, such as usernames, legal names, or social security numbers. From a strictly technical perspective, identifiers distinguish from persona since they concern authentication data for a particular individual or persona.
Therefore, if “Identity” means “being unique”, it depends on gender, age, weight, nationality, and verify credentials such as citizenship, passport, university degree, ID card, membership cards, driving license, store receipts, boarding passes, etc. For example, your wallet is a container of credentials. What is the purpose of credentials? If properly designed, credentials are “safe places”, where verifiable data are allowed in workflows without involving centralized hubs or live communication between the connectors. If “having an identity” means “being unique” supported by “credentials”, which are “safe places” to keep your “identity’s sides”, which is their relation to digital identity?
Before clarifying that correlation, another concept plays an essential role in understanding the importance of digital identities: the trust triangle.
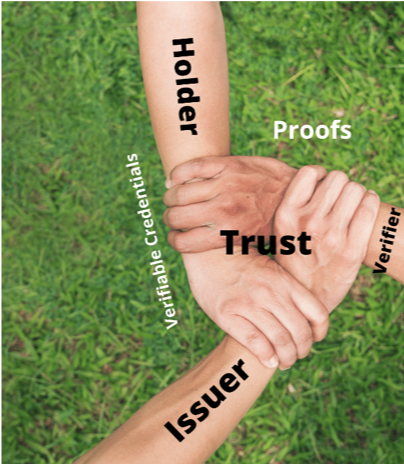
The trust triangle works based on the relationship between the issuer, holder, and verifier. The issuer decides which credentials are to issue and how to validate it to make them trustable and credible. The holder decides which credentials they need to make things reliable about themselves. Finally, verifiers determine who to trust or not, thanks to the proofs they have. How we can see from the picture, we have a first approach of interoperability between entities.
Self-sovereign identities (SSI) in the Internet world own their digital and analog identities and able to control the data that is shared and used. This makes the Internet identifying regime more flexible, secure, private, less burdensome, and cost-saving. The SSI community stores cryptographic public-keys belonging to institutions which already carry trust (such as the DMV or health offices) on a blockchain such as hyperledger indy. The institution can then become an issuer of decentralized identifiers (DID). DIDs are real-world identities such as a covid-immunity-pass or passport or a phone number, which are legal and have practical implications. DID are verifiable for themselves and do not depend on any centralized registers or certificate authorities. In other words, they are identifiers for self-sovereign digital identities. In order to be verifiable, DIDs in their default form never have to be stored on any public database in order to be verifiable.
Blockchain-based digital identity

Heading back to the concept of a blockchain-based digital identity, we must consider that one fundamental aspect of any blockchain-based identity is that it ultimately possesses or controls the private keys necessary to execute a transaction. We need a blockchain to prevent identity hacks and fraud. What are the benefits? Digital identities are expected to grow significantly worldwide in the next 10 years, which is supposed to make a significant contribution to the global economy.
Which companies are involved in this field?
The blockchain solutions have, however, an impact on the economy and industries. Since monetization is a struggle and SSI is still very embryonic, and solutions are still in their early stages the rollout of a global SSI infrastructure requires a unified effort of the biggest corporations as well as government entities in the world which would benefit from a world with SSI. The initiatives below are working on just that just that and with their implementation of DIDs on top of hyperledger Indy may have the ultimate solution to “digital identity”:
- ID2020
- DIF
- Sovrin
- Trust Over IP Foundation
However, even if they have already been working on an SSI solution, they need to move faster and adapt to modern times. Interoperability: This is what companies are trying to do to find a standard solution and defeat invisible enemies. With the emerging dominance of the W3C DID standard, individual identity providers such as Onfido, Jumio and even supply-chain focused solutions which involve digital identity such as the secure certificate of [FP]-LIMS (LIMS software solution designed by the German company Fink & Partner GmbH) will have to adopt the DID standard in order to plug into the emerging global digital identity network since not just personas but even products and devices will eventually be identified using DIDs.
What is the problem? As long as identities stay pretty much physical, the problem persists. How can a technological framework adapt to such a human component? If we think about turning identities into “digital identities”, we must consider that the Internet was designed to connect machines, not human beings, therefore it has to be very flexible to reflect the huge human diversity! That is why companies need to adapt to the SSI protocol.
Conclusion
To sum up, owning a “digital identity” is proof of credibility. What makes you feel safe makes you also trustable: this is essential nowadays due to the restricted human contact. Therefore, interoperability, adopting, and developing the SSI family of protocols is crucial in facing invisible enemies and gaining more credibility and trust by clients.
Related: